If you visit a website with broken external links, that site might have been compromised by cybercriminals looking to damage reputations and scam you.
Securing your network should be a deliberate and continuous effort. Cyberattacks can spring up from the least expected areas. Even the invalid links that are of no use to you can be an attacker’s ticket to break into your system through broken link hijacking.
So what does broken link hijacking actually mean? What are the risks associated with it? And how can you protect your own site from it?
What Is Broken Link Hijacking?
Broken link hijacking involves an attacker taking over your abandoned, expired, or invalid external links, and using them for malicious or fraudulent activities.
An active website will likely include several external links that serve different purposes. Over time, some of these links could expire and you may not be aware of them. You continue running your website, oblivious of the expired links.
Since cyberattackers are constantly looking out for vulnerabilities in systems to penetrate, they come across expired or abandoned links and exploit them for their own gains.
How Does Broken Link Hijacking Happen?
There’s a tendency for one to think that an invalid link is harmless. If you aren’t using it, it serves no purpose, right? But broken link hijacking shows that every link is important, whether active or not.
For instance, your website has an external link to a web analytics service provider. After some time, you switch to another web analytics service provider. Since you no longer use the previous one, you abandon the link.
The link may no longer be useful to your website, but it’s still active and getting traffic. An attacker discovers this and takes possession of the link. They could use this to exploit you and your readers.
Risks Associated With Broken Link Hijacking
Every cyberattack has its consequences. As the network or system owner, you are at the receiving end. Broken link hijacking is no exception.
Once attackers have access to your links, they maximize the opportunity, often at the detriment of your personal or business brand.
Here are a few risks that can arise if you leave your site open to broken link hijacking.
1. Defacement
Changing what your website looks like or promotes via external links can ruin your reputation. For instance, if your web link expires and the attacker purchases the associated domain, they may upload content that is totally different from your original content. Such content could be offensive, fraudulent, or malicious, and against your values.
Since the content is on a page that was originally yours, the audience would be deceived into thinking that you were the one that posted it.
2. Impersonation
The person who has access to an account or page controls what’s posted on it. Through this, cybercriminals can impersonate their victims.
Impersonation is more prevalent with celebrities or public figures. This category of people is influential and usually has a high following.
When an attacker takes over an abandoned web page or social media account of a public figure, they pretend to be the original owner and publish malicious content. Since the followers of these public figures hold them in high esteem, they may heed the instructions of the content before they realize that their role model is being impersonated.
3. Stored XSS
Like most websites, yours might have scripts embedded from third-party applications to enhance the user experience. If the third-party application goes out of business, you’ll have a broken JavaScript link on your page.
Once an attacker leverages this vulnerability, they could insert malicious scripts that are loaded when a user visits that page. A cross-site scripting attack could be happening right under your nose without your knowledge.
How to Prevent Broken Link Hijacking
Having understood the dynamics of broken link hijacking, what can you do to prevent it?
You need to stay on top of your cybersecurity game and secure your web applications so readers can enjoy your site without worrying about cyberattacks and vulnerabilities. Fortunately, broken link hijacking can be prevented with the right defense mechanism.
1. Regularly Scan for Vulnerabilities
One of the biggest concerns of broken link hijacking is that it could be happening right now and you wouldn’t be aware of it. Since attackers penetrate your network by leveraging expired, invalid, or abandoned links, you can prevent this form of attack by scanning your website to detect vulnerabilities including broken links.
An effective vulnerability scanner shows you all your links and their status, whether they are active or not. From the results at your disposal, ensure that you delete any link that isn’t active from your system.
Check the sources of all your external links to confirm that they are connected to the correct web pages and not one managed by hackers.
2. Implement SubResource Integrity
In broken link hijacking, your browser is misled to continually process compromised links. And because the links were originally generated from your website, they come across as genuine.
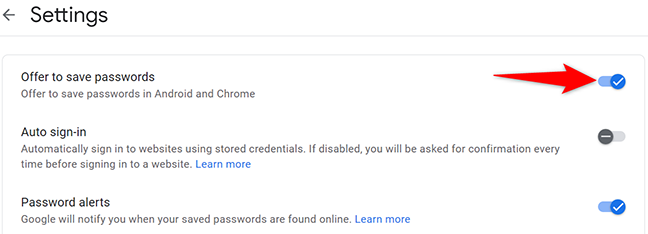
Implementing SubResource Integrity (SRI) comes in handy because it checks the authenticity of links being processed. It ensures that only links that haven’t changed in their form or style since they were published are loaded on your browser.
In SRI, a cryptographic hash of the content is curated and added to the <script> or <link> code through the integrity value.
Instead of processing a script right away, your browser makes a comparison between the requested command and the established integrity hash value. If the hashes aren’t a match, it discards the request.
3. Add Content Security Policy
You can examine the domains that resources are loaded from by adding a content-security-policy HTTP header to your server’s responses. For instance: Content-Security-Policy: default-src ‘self’ yoursite.net *.yoursite.org
In this example, commands including style sheets, scripts, and images can only be initiated from the site’s origin (self—with the exclusion of subdomains) and yoursite.net (subdomains are excluded).
A content security policy prevents your browser from loading resources that are from unknown or from unverified sources. Every resource that makes it through your browser is certified to be authentic.
Prioritize the Security of All Your Links
You can direct users to your other pages, services, or products externally by embedding their links on your website. While this is common practice, threats like broken link hijacking mean that you need to pay more attention to your links.
The internal links on your site may seem more useful to you and take a lot of your attention, but don’t focus on them to the detriment of your external links.
Give priority to both your internal and external links. If your external links are hijacked, the internal links that you value so much will be directly or indirectly compromised.
For more such interesting article like this, app/softwares, games, Gadget Reviews, comparisons, troubleshooting guides, listicles, and tips & tricks related to Windows, Android, iOS, and macOS, follow us on Google News, Facebook, Instagram, Twitter, YouTube, and Pinterest.